This is the Only Reliable Means of Protecting Critical Infrastructure

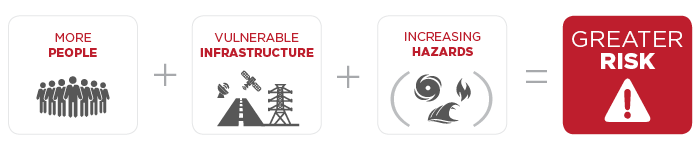 More people and vulnerable infrastructure exposed to more frequent and intense hazards equals even greater risk for us in the future. The time to rethink the equation is now.[1]
More people and vulnerable infrastructure exposed to more frequent and intense hazards equals even greater risk for us in the future. The time to rethink the equation is now.[1]
When organizations consider the approach to protection, they naturally gravitate to questions, such as “what do I need to protect?” and “how can I protect those things?” The question of what to protect is difficult. It takes a degree of perspective, prioritization, and foresight that is difficult for most individuals and
nearly impossible for groups seeking consensus. Once protection needs are clear, organizations need to address the question of how to protect those priorities. This consideration is even more complicated, especially for those tasked with protecting our critical infrastructure.
In an environment of increasingly limited resources, organizations face difficult tradeoffs. How can they protect against multitudes of risks, ranging from existential events like hurricanes to more pervasive occurrences like insider threat? As is so often the case, the answer to this pressing dilemma is strategy and process.
History (distant and current) highlights three critical attributes any successful threat protection program must be: Consistent, Insistent, and Persistent. For those in Critical Infrastructure Protection, the acronym should be easy to remember – CIP.
Consistent: Possessing firmness or coherence; marked by harmony, regularity, or steady continuity; free from variation or contradiction; tending to be arbitrarily close to the true value of the parameter estimated as the sample becomes large
Insistent: Disposed to insist; compelling attention
Persistent: Existing for a long or longer than usual time or continuously; continuing without change in function or structure; continuing or inclined to persist
A threat protection program demands continuity, buy-in, and longevity to establish its usefulness. Ironically, the recent hurricane offers proof of this (unfortunate but highly useful) fact.

It’s been 12 years since Hurricane Katrina hit New Orleans. That event was an inflection point for many organizations. Responses by public and private entities in the immediate aftermath and over the past decade have exposed a host of lessons about the necessity for strong critical infrastructure. On August 25, 2017, Hurricane Harvey tested the progress as it unleashed the worst natural disaster experienced on U.S. soil.
While it’s too early to assess the long-term human, ecological, economic, and other impacts of Hurricane Harvey, we know a few things. Roads, energy supply, and water management systems were struck hard. The city is a hub of enterprise and energy production – any compromise to those market centers is, will continue to be felt across the city, the state, the U.S., and the world. The response to Hurricane Harvey has served to highlight the critical importance of protecting infrastructure – whether it is people, pipes, or petabytes.
“We need to build and modernize infrastructure to make our water management systems more resilient to both floods and droughts. We must continue to invest in the weather forecasting systems that provided advance warning and in the public services that build community resilience and provide disaster response.
Here again Texas can lead the way. We’re already number one in wind power production by state, thanks to targeted investments that boosted the power grid connecting cities with windy regions. And we’ve only begun to tap our abundant solar resources.
The innovations that energy companies have pioneered to build offshore oil platforms can inform the development of, and investment in, offshore wind turbines and their knowledge of producing petrochemicals could be applied to more sustainably produced biofuels.
Today, wind and solar power prices are now competitive with fossil fuels across Texas.”[2]
This conversation took place between a group of experts representing the National Science Foundation, NASA, the EPA, Texas Commission on Environmental Quality, the Department of the Interior, and the Department of Transportation. It shows how a strategic CIP group has focused on protecting the numerous facets of critical infrastructure in the state. They have worked over time with Consistency, Insistency, and Persistency. The result is a high level of optimism about the capacity for this region to recover.
Building a CIP Approach for your Organization
People are creatures of habit. We naturally prefer simple patterns. (Most of us follow the same process every morning to get ready for work.) Organizations should seek to do the same with their security and protection policies: consistent policies help people understand what they are supposed to protect and how to protect them, regardless of the fluctuation of risk types.
To establish the right behaviors, however, consistent policies are insufficient. When it comes to security and protection, you can’t overlook the role of senior leadership. The C-suite must be insistent in how and where they enforce the policies. They set the example by holding themselves accountable, and then take steps to hold others accountable.
Together, consistent policies and insistent leadership must be persistent in the face of various, expected, and unexpected challenges. For real security behaviors to become a part of an organization’s culture, its people must know that the organization will stand by the policies and support the people trying to implement them.
And even still, Consistency, Insistency, and Persistency are irrelevant if you lack the right practices and procedures for protecting their valuable assets. Policies and protocols must be current, and the organization must consistently pursue advanced methods available to protect assets. As you evaluate the sufficiency of your CIP approach, begin with a few fundamental considerations:
- What are the existing high-risk areas (i.e., personnel, policies, physical, etc.) within the organization’s infrastructure?
- What are the outdated assumptions on protection?
- How are other organizations incorporating alternative protective measures?
- How will leaders, and the workforce, adapt the necessary changes?
- What is the culture required to successful protect CIP?
No matter your industry, you will need to consider all aspects of your critical infrastructure – people, pipes, and petabytes. Toffler Associates’ CIP for CIP analytical process will help you define your critical assets, identify the threats and vulnerabilities, and design a culture that supports a Consistency, Insistency, and Persistency approach to protecting them.
It’s time to engage a consistent, structured approach to building resilience for the future.
{{cta(‘c254ce44-075c-42d8-8fb5-4887c026f5c7’)}}
[1] Andrew Dessler, Texas A&M University ; Daniel Cohan, Rice University, and Katharine Hayhoe, Texas Tech University – Excerpted from What Hurricane Harvey says about risk, climate and resilience, The Conversation and Houston Chronicle, September 1, 2017
[2] Andrew Dessler, Texas A&M University ; Daniel Cohan, Rice University, and Katharine Hayhoe, Texas Tech University – Excerpted from What Hurricane Harvey says about risk, climate and resilience, The Conversation and Houston Chronicle, September 1, 2017
- Categories
- Security and Resilience
- Strategic Planning


 About the Authors
About the Authors